svchost.exe is one of the oldest processes, first introduced by Microsoft on Windows 2000. In this technical article, you will learn what it is and what it does svchost.exe on Windows.
svchost.exe, can be considered the father of all processes present on Windows. From Windows 2000 and up to Windows 11, you can find this service in Task Manager.
If you are going to open Task Manager in the tab dedicated to processes (Processes), You will notice that svchost.exe is currently multiple instances which running simultaneously. Most users who see the multitude of processes svchost.exe, they think of viruses and malware.
Content
What it is and what it does svchost.exe on Windows
svchost.exe (Service Host) is a generic operating system process Windows which hosts and runs system services. For Windows uses a modular architecture, with different services constantly running in the background, svchost.exe it helps to organize and group similar services into separate processes, to save system resources and improve performance. This being the reason why in Task Manager you will notice several instances of this process.
When a system service needs to be executed, svchost.exe create a new process to host that service. Several services can be grouped in a single process svchost.exe, which allows the operating system to have more precise control over the system resources used by these services.
Could svchost.exe be a virus?
Now, svchost.exe it cannot be a virus, but it can be used as a vector for computer attacks.
It is important to mention that, though svchost.exe is an important operating system process Windows, this can also be an attack vector for malware or malicious programs that can infect or take control of the process and, therefore, gain access to system resources and user data.
Therefore, it is important to verify the authenticity and integrity of the process svchost.exe and associated services, through an antivirus or other security tools.
Performance optimization Windows with svchost.exe
svchost.exe was introduced to manage system services more efficiently and allow better use of system resources. Before Windows 2000, each service was managed by a separate process, which led to greater resource fragmentation and lower performance.
With the introduction of the process svchost.exe, services can be grouped and managed in a common process, which can reduce the number of processes running in the background and improve system performance. Also, svchost.exe helps to ensure a higher level of security, by managing services centrally and by restricting access to the system resources used by them.
In conclusion, the process svchost.exe is an important element of the system architecture Windows and is used to manage and organize system services in a more efficient way.
Services managed by svchost.exe
svchost.exe can host multiple system services Windows simultaneously, to reduce resource fragmentation and save memory space.
Here are some examples of services that can be loaded in svchost.exe, to better understand what svchost.exe does on Windows:
- Services RPC (Remote Procedure Call) - allow communication between processes on operating systems Windows.
- Windows Update – managing system updates and downloading and installing security and other updates.
- Encryption services – management of digital certificates and data encryption on systems Windows.
- Windows Firewall – managing security regulations for network traffic.
- Audio Services Windows – management of sound and audio devices on the systems Windows.
- Services Print Spooler – management of printers and print queues.
- Services Windows Management Instrumentation (WMI) - providing information about the system, such as hardware, software and configuration.
- Services Windows Error Reporting - providing reports on errors and system problems to Microsoft.
- Service Windows Installer - managing the installation, repair and uninstallation of applications and software packages.
- Network services – management of network connections and communications, such as service DHCP (Dynamic Host Configuration Protocol), service DNS (Domain Name System), file transfer service (FTP) and other.
- Security services – management of user authentication and authorization, as well as data encryption and decryption. These services include the service Windows Defender, service BitLocker, service Smart Card and others.
- Administration services – management of system administration and maintenance activities, such as event management, management of system maintenance and update services, as well as backup and restoration services.
- Multimedia services – management of multimedia devices, such as web cameras, microphones, speakers and other sound and image capture and playback devices.
- Programming services – managing processes that require programming, such as the service of Task Scheduler and the service of indexing services Windows.
- User interaction services – managing user interaction, such as the theme service and the notification service.
These are just some of the examples of services that can be uploaded svchost.exe operating systems Windows.
How can you see the svchost.exe service groups?
The service groups that use the svchost.exe processes can best be seen in Command Prompt.
Go to the Menu Start -> Run -> type “cmd”And press Enter. After the window opens Command Prompt, type: tasklist /SVC and press enter.
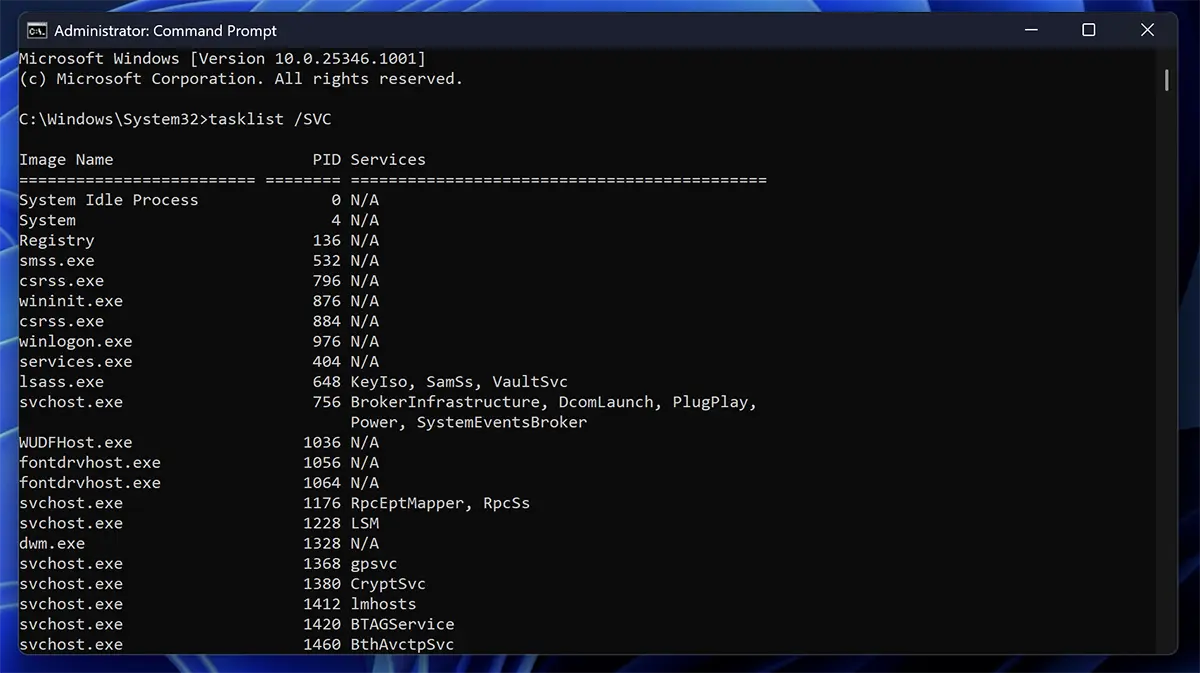
It is important to remember that, depending on the version of Windows and system configuration, certain services can be managed by separate processes or other svchost.exe groups.
क्या svchost.exe से हमारे computer / PC को हैक कर सकता है कोई |